Data Communication and Networking
Category : Banking
Data Communication and Networking
The term communication means sending or receiving information. When we communicate, we share information or data. A communication system can be defined as the collection of hardware and software that facilitates intersystem exchange of information between different devices.
Data Communication
It is the exchange of data between two devices using some form of transmission media. It includes the transfer of data or information and the method of preservation of data during the transfer process. Data is transferred from one place to another in the form of signals. There are three types of signals
Communication Channel
The communication channel refers to the direction of signal flow between two linked devices.
Types of Communication Channel
There are mainly three types of communication channel
(i) Simplex Channel In this channel, the flow of data is always in one direction, with no capability to support response in other direction. This communication is unidirectional. Only one of the communicating devices transmits information and the other can only receive it. e.g. Radio, Television, Keyboard, etc.
(ii) Half Duplex Channel In this channel, the data can flow in both directions, but not at a same time. When one device transmits information, then other can only receive at that point of time. e.g. Walkie-Talkie.
(iii) Full Duplex Channel In this channel, the How of data is in both directions at a time, i.e. both stations can transmit and receive information simultaneously, e.g. Wireless handset (mobile phone).
Communication Media
Communication media of a network refer to the transmission media or the connecting media used in the network. It can be broadly defined as anything that can carry information from a source to destination. It refers to the physical media through which communication signals can be transmitted from one point to another.
Transmission media can be divided into two broad categories
Guided Media or Wired Technologies
The data signal in guided media is bound by the cabling system that guides the data signal along a specific path. It consists of a cable composed of metals like copper, tin or silver.
Basically, they are divided into three categories
(i) Ethernet Cable or Twisted Pair In this pair, wires are twisted together, which are surrounded by an insulating material and an outer layer called jacket. A twisted pair consists of two conductors (copper). One of the wires is used to carry signals to the receiver and the other is used only as a ground reference. It is used as a short distance communication, e.g. Local area networks use twisted pair cable.
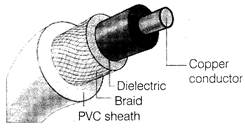
(ii) Co-axial Cable It carries the signal of higher frequency data communication through the network. It consists of a solid wire core surrounded by foil shielded or conducting braid or wire mesh, each separated by some insulator. It has a single inner conductor that transmits electric signals and the outer conductor acts as a ground and is wrapped in asheath of teflon or PVC. Co-axial cable is commonly used in transporting multi-channel television signals in cities, e.g. Cable TV network.
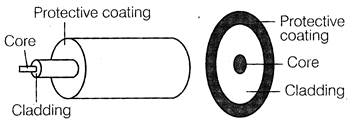
(iii) Fibre Optic Cable It is made up of glass or plastic and transmits signals in the form of light from a source at one end to another. At the source, there are either Light Emitting Diodes (LEDs) or Laser Diodes (LDs), which modulate the data into light beam using frequency modulation techniques.
Optical fibres allow transmission over longer distance at higher bandwidth which is not affected by electromagnetic field. The speed of optical fibre is hundred of times faster than co-axial cables.
Unguided Media or Wireless Technologies
It is the transfer of information over a distance without the use of enhanced electrical conductors or wires. When the computers in a network are interconnected and data is transmitted through waves, then they are said to be connected through unguided media. Some commonly used unguided media of transmission are
(i) Radiowave Transmission When two terminals communicate by using radio frequencies then such type of communication is known as radiowave transmission. This transmission is also known as Radio Frequency (RF) transmission. These are omnidirectional. Radiowaves, particularly those waves that propagate in the sky mode, can travel long distances. Each computer attaches to an antenna that can both send and receive radio transmission.
(ii) Microwave Transmission Microwaves are electromagnetic waves having frequencies range from 0.3 to 300 GHz. Microwaves are unidirectional. Microwaves have a higher frequency than that of radiowaves.
Microwave is one of the fastest media for data transmission over communication channel. They can be aimed at a single direction instead of broadcasting in all direction. Microwave antenna placed on the top of buildings. It consists series of stations approx. 30 miles apart. It is used in cellular network and television broadcasting.
(iii) Infrared Wave Transmission Infrared waves are the high frequency waves used for short-range communication. These waves do not pass through the solid-objects. They are mainly used in TV remote, wireless speakers.
(iv) Satellite Communication The communication across longer distances can be provided by combining radio frequency transmission with satellites. It works over a long distance and fast communication. Satellite communication amplifies signal received from one Earth station and again, retransmits to another Earth station, which can be located many thousands of miles away. It is used for communication to ships, vehicles, planes and handheld terminals.
Tit-Bits
Computer Network
It is a collection of two or more computers., which are connected together to share information and resources. Computer network is a combination of hardware and software that allows communication between computers over a network.
Benefits of Networking
Some of the benefits of network are discussed below
(i) File Sharing Networking of computer helps the users to share data files.
(ii) Hardware Sharing Users can share devices such as printers, scanners, CD-ROM drives, hard drives, etc.
(iii) Application Sharing Applications can be shared over the network and this allows implementation of client/server applications.
(iv) User Communication This allows users to communicate using E-mail, newsgroups, video conferencing within the network.
Types of Computer Network
Computer network is broadly classified into various types
Local Area Network (LAN)
LAN is a small and single-site network. It connects network devices over a relatively short distance. It is a system in which computers are interconnected and the geographical area such as home, office, buildings, school may be within a building to 1 km. On most LANs, cables are used to connect the computers. LANs are typically owned, controlled and managed by a single person or organisation. They also use certain specific connectivity technologies, primarily Ethernet and Token Ring. LAN provides a sharing of peripherals in an efficient or effective way.
Wide Area Network (WAN)
A WAN is a geographically dispersed collection of LANs. A WAN like the Internet spans most of the world. A network device called a router connects LANs to a WAN. Like the Internet, most WANs are not owned by any one organisation, but rather exist under collective or distributed ownership and management. WANs use technology like ATM, Frame Relay and X.25 for connectivity.
Metropolitan Area Network (MAN)
It is a data network designed for a town or city. It connects an area larger than a LAN, but smaller than a WAN, such as a city, with dedicated or high performance hardware.
Its main purpose is to share hardware and software resources by the various users. Cable TV network is an example of metropolitan area network. The computers in a MAN are connected using co-axial cables or fibre optic cables.
Personal Area Network (PAN)
PAN refers to a small network of communication. These are used in a few limited range, which is in reachability of individual person. Few examples of PAN are Bluetooth, wireless USB, Z-wave and Zig Bee.
Virtual Private Network (VPN)
VPN is a technology that is gaining popularity among large organisations that use the global Internet for both intra-and inter-organisation communications, but require privacy in their intra-organisation communication. VPN is a network that is private but virtual.
It is private because it guarantees privacy inside the organisation. It is virtual because it does not use real private WANs; the network is physically public but virtually private.
Network Devices
These devices are required to amplify the signal to restore the original strength of signal and to provide an interface to connect multiple computers in a network. There are many types of network devices used in networking.
Some of them are described below
Repeater
It is a device that operates only on the physical layer of OSI model. Repeaters have two ports and can connect two segments of a LAN. It amplifies the feeble signals when they are transported over a long distance so that the signal can be as strong as the original signal. A repeater boosts the signal back to its correct level.
Hub
It is like a repeater with multiple ports used to connect the network channels. It acts as a centralised connection to several computers with the central node or server. When a hub receives a packet of data at one of its ports from a network channel, it transmits the packet to all of its ports to all other network channel.
Gateway
It is an interconnecting device, which joins two different network protocols together. They are also known as protocol converters. It accepts packet formated for one protocol and converts the formated packet into another protocol.
The gateway is a node in a network which serves as a proxy server and a firewall system and prevents the unauthorised access. It holds the information from a Website temporarily, so that the repeated access to same Website or Web page could be directed to the proxy server instead of actual web server. Thus helps in reducing the traffic load.
Switch
It is a small hardware device that joins multiple computers together within one LAN. Switches work on the data link layer of the OSI model. It helps to reduce overall network traffic.
Switch forwards a data packet to a specific route by establishing a temporary connection between the source and the destination. There is a vast difference between a switch and a hub. A hub forwards each incoming packet (data) to all the hub ports, while a switch forwards each incoming packet to the specified recipient.
Router
It is a hardware device which is designed to take incoming packets, analyse the packets, moving and converting the packets to another network interface, dropping the packets, directing packets to the appropriate locations, etc.
Bridge
It serves a similar function as switches. A bridge filters data traffic at a network boundary. Bridges reduce the amount of traffic on a LAN by dividing it into two segments. Traditional bridges support one network boundary, whereas switches usually offer four or more hardware ports. Switches are sometimes called multiport bridges.
Modem
It is a device that converts digital signal to analog signal (modulator) at the sender's site and converts back analog signal to digital signal (demodulator) at the receiver's end, in order to make communication possible via telephone lines. A MODEM is always placed between a telephone line and a computer.
Network Topology
The term 'topology' refers to the way a network is laid out, either physically or logically. Topology can be referred as the geometric arrangement of a computer system. Each computer system in a topology is known as node. Network topology is determined only by the configuration of connections between nodes. The most commonly used topology are described below
Bus Topology
It is such that there is a single line to which all nodes are connected. It is usually used when a network, installation is small, simple or temporary. In bus topology, all the network components are connected with a same (single) line. Ethernet is commonly well protocol in networks connected by bus topology.
Advantages
(a) All the nodes are connected directly, so very short cable length is required.
(b) The architecture is very simple and linear.
(c) Bus topology can be extended easily on either sides.
Disadvantages
(a) In case of any fault in data transmission, fault isolation is very difficult. We have to check the entire network to find the fault.
(b) Becomes slow with increase in number of nodes.
(c) The entire network shuts down if there is an error occurs in the main cable.
Star Topology
In this network topology, the peripheral nodes are connected to a central node, which rebroadcasts all transmissions received from any peripheral node to all peripheral nodes across the network, including the originating node. A star
network can be expanded by placing another star hub.
The protocols used in star topology are Ethernet, Token Ring and Local Talk.
Advantages
(a) Installation of star topology is very easy as all the nodes are directly connected to the central node or server.
(b) Easy to detect faults and remove it.
(c) Failure of single system will not bring down the entire network.
Disadvantages
(a) Requires more cable length than bus topology.
(b) If hub or server fails, the entire network will be disabled.
(c) Difficult to expand, as the new node has to connect all the way to central node.
Ring or Circular Topology
This topology is used in high-performance networks where large bandwidth is necessary.
The protocols used to implement ring topology are Token Ring and Fiber Distributed Data Interface (FDDI). In ring topology, data is transmitted in form of Token over a network. After passing through each node, the data returns to the sending node.
Advantages
(a) Short cable length is required.
(b) Suitable for optical fibre as the data flow in one direction.
(c) It is less costly than star topology.
Disadvantages
(a) Fault diagnosis is very difficult in a network formed using ring topology.
(b) Failure of single computer affects the whole network.
(c) Adding or removing the computers disturbs whole network activity.
Mesh Topology
It is also known as completely interconnected topology. In mesh topology, every node has a dedicated point-to-point link to every other node.
It provides a bi-directional link between each possible node. This type of network topology contains atleast two nodes with two or more paths between them. Mesh topology is robust because the failure of any one computer does not bring down the entire network.
Advantages
(a) Excellent for long distance networking.
(b) Communication possible through the alternate route, if one path is busy.
(c) Its performance is not affected with heavy load of data transmission.
Disadvantages
(a) Long wire/cable length, hence increase in the cost of installation and maintenance.
(b) The hardware required to connect each link is expensive.
Tree Topology
This is a network topology in which nodes are arranged as a tree. The function of the central node in this topology may be distributed. A tree topology is an extension and variation of star topology. Its basic structure is like an inverted tree, where the root acts as a server. It allows more devices to be attached to a single hub.
Advantages
(a) The tree topology simulates hierarchical flow of data. So, it is suitable for applications where hierarchical flow of data and control is required.
(b) We can easily extend the network.
(c) If one segment is damaged, other segments are not affected.
Disadvantages
(a)Long cables are required.
(b)There are dependencies on the root node.
(c) If the central hub fails, the entire system breaks down.
Models of Computer Networking
There are mainly two models of computer networking
Peer-to-Peer Network
It is also known as P2P network. This computer network relies on computing power at the edges of a connection rather than in the network itself.
It is used for sharing content like audio, video, data or anything in digital format. In P2P
connection, a couple of computers is connected via a Universal Serial Bus (USE) to transfer files.
In peer-to-peer networking, each or every computer may be worked as server or client.
Client-Server Network
The model of interaction between two application programs in which a program at one end (client) requests a service from a program at the other end (server). It is a network architecture which separates the client from the server. It is scalable architecture. where one computer works as server and others as client. Here, client acts as the active device and server behaves as passively.
OSI Model
Open System Interconnection (OSI) is a standard reference model for communication between two end users in a network. In 1983, the International Standards Organisation (ISO) published a document called Basic Reference Model for Open System Interconnection, which visualises network protocols as a seven layered model.
OSI is a layered framework for the design of network system that allows communication between all types of computer system. It is mainly consists of seven layers across a network as shown in table.
Seven Layers of OSI Model and their Functions
|
Name of the Layer |
Functions |
|
Application Layer [User-Interface]
|
Retransferring files of information, login, password Checking, packet filtering etc. |
|
Presentation Layer [Data formatting] |
It works as a translating layer, i.e. encryption or decryption. |
|
Session Layer [Establish and maintain connection] |
To manage and synchronise conversation between two systems. It controls logging ON and OFF, user identification, billing and session management. |
|
Transport Layer[Transmission Control Protocol(TCP) accurate data] |
It decides whether transmission should be parallel or single path, multiplexing, splitting or segmenting the data, to break data into smaller units for efficient handling, packet filtering. |
|
Network Layer [Internet Protocol (IP) routers] |
Routing of the signals, divide the outgoing message into packets, to act as network controller for routing data. |
|
Data Link Layer [Media Access Control (MAC) switches] |
Synchronisation, error detection and correction. To assemble outgoing messages into frames. |
|
Physical Layer [Signals-cables or operated by repeater] |
Make and break connections. define voltages and data rates. convert data bits into electrical signal, Decide whether transmission is simplex, half duplex or full duplex. |
In OSI model physical layer is the lowest layer which is implemented on both hardware and. software and application layer is the highest layer.
Terms Related to Network
You need to login to perform this action.
You will be redirected in
3 sec
