Components of Computer System
Category : Banking
Components of Computer System
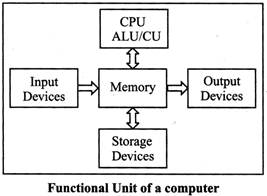
Any computer system consists of the four basic units; namely input unit, storage unit, central processing unit and output unit. Central Processing unit consists of Arithmetic logic unit and Control unit.
A computer performs five major functions no matter what size they are of as follows:
BASIC COMPONENTS OF COMPUTER SYSETEMS
Following are the various components of a computer system-
Input Unit
Data and instructions must enter the computer system before any computation can be performed on the supplied data. The input unit that links the external environment with the computer system performs this task. An input unit performs the following functions:
Output Unit
The job of an output unit is just the reverse of that of an input unit. It supplied information and results of computation to the outside world. Thus it links the computer with the external environment. As computers work with binary code, the results produced are also in the binary form. Hence, before supplying the results 10 the outside world, it must be converted to human acceptable (readable) form. This task is accomplished by snits called output interfaces.
Following functions are performed by an output unit.
Storage Unit
The data and instructions that are entered into the computer system through input units have to be stored inside the computer before the actual processing starts. Similarly, the results produced by the computer after processing must also be kept somewhere inside the computer system before being passed on to the output units. The Storage Unit or the primary / main storage of a computer system is designed to do all these things. It provides space for storing data and instructions, space for intermediate results and also space for the final results. The specific functions of the storage unit are to store:
Central Processing Unit
The main unit inside the computer is the CPU. This unit is responsible for all events inside the computer. It controls all internal and external devices, performs "Arithmetic and Logical operations". The operations a Microprocessor performs are called "instruction set" of this processor. The instruction set is "hard wired" in the CPU and determines the machine language for the CPU. The more complicated the instruction set is, the slower the CPU works. Processors differed from one another by the instruction set. If the same program can run on two different computer brands they are said to be compatible. Programs written for IBM compatible computers will not run on Apple computers because these two architectures are not compatible.
The control Unit and the Arithmetic and Logic unit of a computer system are jointly known as the Central Processing Unit (CPU). The CPU is the brain of any computer system. In a human body, all major decisions .are taken by the brain and the other parts of the body function as directed by the brain. Similarly, in a computer system, all major calculations and comparisons are made inside the CPU and the CPU is also responsible for, activating and controlling the operations of other units of a computer system.
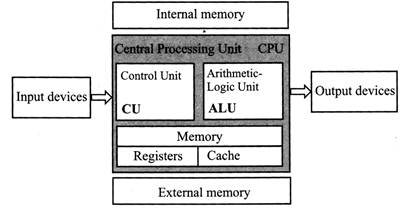
Arithmetic and Logic Unit (ALU)
The arithmetic and logic unit (ALU) of a computer system is the place where the actual execution of the instructions take place during the processing operations. All calculations are performed and all comparisons (decisions) are made in the ALU. The data and instructions, stored in the primary storage prior to processing are transferred as and when needed to the ALU where processing takes place. No processing is done in the primary storage unit. Intermediate results generated in the ALU are temporarily transferred back to the primary storage until needed at a later time. Data may thus move from primary storage to ALU and back again as storage many times before the processing is over. After the completion of processing, the final results which are stored in the storage unit are released to an output device.
The arithmetic and logic unit (ALU) is the part where actual computations take place. It consists of circuits that perform arithmetic operations (e.g. addition, subtraction, multiplication, division over data received from memory and capable to compare numbers (less than, equal to, or greater than).
Control Unit
The control unit directs and controls the activities of the internal and external devices. It interprets the instructions fetched into the computer, determines what data, if any, are needed, where it is stored, where to store the results of the operation, and sends the control signals to the devices involved in the execution of the instructions. By the help of control unit, ALU known what should be done with the data, once it is received data then, how is it that only the final results are sent to the output devices and the control unit is also able to maintain order and directs the operation of the entire system.
Register: In a computer, a register is one of a small set of data holding places that are part of a computer processor. A register may hold a computer instruction, a storage address, or any kind of data (such as a bit sequence or individual characters).
COMPUTER DEVICES
Computer devices are divide into two parts: (i) Input Device (ii) Output device
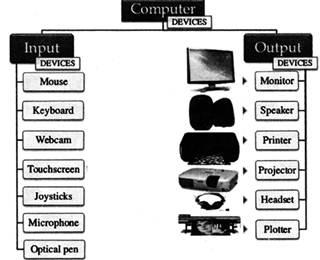
Input Devices
Input devices include those devices with the help of which we enter data into computer as they make a link between user and computer. These devices translate the human readable information into the form understandable by computer. The various devices are as follows -
The keys are following:
|
Sr. No |
Keys |
Description |
|
1. |
Typing Key |
These keys include the letter keys(A-Z) and digits keys(0-9) |
|
2. |
Numeric Keypad |
It is used to enter numeric data or cursor movement. It has a set of 17 keys that are in the same layout as that of calculators. |
|
3. |
Function Keys |
There are twelve functions keys present on the keyboard. These are arranged in a row along the top of the keyboard. Each function key has unique meaning and is used for some specific purpose. |
|
4. |
Control keys |
These keysare used to provide cursor and screen control. It includes four directional arrow key. Control keys also include Home, End, Insert, Delete, Page Up, Page Down, Control (Ctrl), Alternate (Alt), Escape(Esc). |
|
5. |
Special Purpose |
Keyboard also contains some special purpose keys such as Enter, Shift, Keys Caps Lock, Num Lock, Space bar, Tab, and Print Screen. |
Smart cards are used for a variety of purposes, including:
-Storing a patient's medical records
-Storing digital cash
-Generating network IDs (similar to a token)
To use a smart card, either to pull information from it or add data to it, you need a smart card reader, a small device into which you insert the smart card.
Output Devices
An output device is that component of computer hardware that communicates the results of data that is processed by the computer and converts the digital information into a form easily read and understood by humans. Various Output devices are used in Computers.
Two kinds of viewing screens are used for monitors:
(a) Cathode-Ray Tube (CRT) Monitor: In the CRT, display consists of small picture elements known as pixels and determine the resolution of the image. Smaller are the pixels the better is the image clarity or resolution. Finite number of characters can be displayed on a screen at once. The screen can be divided into a series of character boxes that serve as a fixed location on the screen where a standard character can be placed. Most screens are capable of displaying 80 characters of data horizontally and 25 lines vertically, CRT has some disadvantages as
(i). It is large in Size
(ii). Has a high power consumption.
Flat-Panel Display Monitor: The flat panel displays overcome the disadvantages of CRT as they have reduced volume, weight and power requirement compared to the CRT. They come in different shapes and size. You can hang them on walls or wear them on your wrists. They are used in all modem day calculators, video games, monitors, laptop computer, graphics display etc. as displays.
The flat-panel display are of two main types:
(i) Emissive Displays: The emissive displays convert electrical energy into light. Example are plasma panel and LED (Light-Emitting Diodes).
(ii) Non-Emissive Displays: The Non-emissive displays use optical effects to convert sunlight or light from some other source into graphics patterns. Example is LCD (Liquid-Crystal Device).
(c) 3-D Monitors: It is a television that conveys depth perception to the viewer. 3-D describes an image that provides the perception of length. When 3-D images are made interactive then user feel involved with the scene and this experience is called virtual reality.
Printers: Printer is among the most common output device, which is used to print information on paper. There are two types of printers:
(a) Impact Printers: The printers that print the characters by striking against a ribbon and then onto the paper, are called impact printers.
Impact Printers are low of cost but they happen to be very noisy. Due to their low cost they are useful for bulk printing. There is physical contact with the paper to produce an image.
Impact printers can be further divided into two types:
(i) Character printers: These printers print one character at a time. These further divided into two such as the Dot Matrix Printer and the daisy wheel printer.
Dot matrix printer (DMP): They are the most popular printers because of their ease of printing features. They come at a low cost.
Each character is printed in the form of pattern of Dot's and head .These dots and heads consist of a matrix of pins of size (5*7, 7*9, 9*7 or 9*9) that result in forming a character. Hence they
Are called as Dot Matrix Printer.
Disadvantage of Dot Matrix Printer are.
(i) Slow Speed (ii) Poor Quality.
Daisy Wheel: These are known as daisy wheel printers as the head lies on the wheel and Pins correspond to characters like petals of Daisy flower. These printers are used for word-processing in offices and offer very nice quality representation. Disadvantage of Daisy wheel Printer
It is Slower Then DMP, Noisy, (ii) More expensive then DMP.
(ii) Line Printers: Line printers are printers, which print one line at a time. Speed of line printers is limited by the speed of cartridge used.
These can be divided into two types: The drum printer and the Chain printer
Drum Printer: This printer looks like a drum in shape that's why it is called a drum printer. The Drum surface has a number of tracks. Total tracks are equal to size of paper, i.e., for a paper width of 132 characters, Drum will have 132 tracks. A character set is embossed on track. The different character sets available in market are 48 character set, 64 and 96 characters set. One rotation of drum leads to printing of one line. These printers print between300 to2000 lines per minute. Hence they have a very high speed.
Disadvantage of this Printer are:
(i) It is very expensive, (ii) Character fonts can't changed.
Chain Printer: In this printer because chain of character sets are used hence they are called as Chain Printers. A standard character set may have 48, 64, 96 characters. Advantage of chain Printer is character fonts can easily be changed & different language can be used with same printer, less noisy then drum printer.
(b) Non-impact Printers: These printers print the characters without the physical contact with the paper i.e. without striking against the ribbon and onto the paper. These printers print one complete page at a time, and are also called as Page Printers. It is support many fonts & different character size, high quality printing, not noisy, faster then impact printer.
These printers are of two types: Laser Printers and the Ink-jet Printers.
(i) Laser Printers: These are non-impact page printers. They use laser lights to produce the dots needed to form the characters to be printed on a page.
(ii) InkJet Printers: Ink-jet printers are new technology non-impact character printers. They print characters via spraying small drops of ink onto paper. Ink-jet printers produce very high quality output with presentable features.
They are noiseless printers and have many styles of printing modes available. These are also called as the coloured printers. Models of Ink-jet printers can produce multiple copies of printing also.
Some important points-
MAINTAINING COMPUTER SYSETEMS
We must ensure that the computer is well looked after. It can only run smoothly if it is protected valuable from malicious viruses which can wreak havoc on your PC or Mac.
Computers that become overloaded or vulnerable to viruses can freeze or crash. This can lead to loss of information .Hackers who hack professionally can be a threat to the computers. There are some extremely sophisticated and technologically advanced group or individuals who are hackers and can destabilise operating systems and bring computer networks crashing down.
This can lead to a slow computer. Each time a web page is opened or an attachment is downloaded certain data on the computer gets collected, much of it is not needed to be used again .This data gets clogged up on your hard drive and can affect your computer's performance if you don't do a spring clean once .Your computer must be given a general assessment every couple of months. A general assessment should be done more frequently (around once a month) if your computer is used a lot.
Backing Up
It is a very important thing to get into the habit of backing up your files on a regular basis. This means having a recent copy of important data held onto your computer. The important documents on your system include the invoices, legal documents or personal files such as photo albums.
You can copy your files to a USB memory stick. USE memory stick do not have enough data to store. They can be quite expensive to buy. They have been popular because of their portability as they're easy to use.
Disk imaging is one of the most effective methods of backing up .This is a more expensive method as it is the most fail-safe method of restoring everything on your computer if you lose everything on your hard drive. With the advent of various online backup you can enlist to help with the storage of your computer's data, which are incredibly convenient as the backup is done automatically and your files are kept in a safe online environment that you can access at any time.
Deleting files
Storing huge data and big files on your computer can bring performance speeds immediately down. In order to make sure your computer is running efficiently it's important to delete unnecessary files from time to time. Windows operating systems has a disk cleanup function that is extremely quick and easy to use. Disk cleanup doesn't take too long to run .This utility on your computer cleans up all the unwanted files that are stored in your computer's cache.
Scanning your hard drive
It is really important to scan your hard drive as another routine task which you should get into the habit of doing regularly. This utility examines the hard drive for some errors that could have a direct effect on your computer's efficiency. This needs to be done around once a week to use your computer every day or once in a month in case if you use it less frequently.
Defragmenting your hard drive
The computer's hard drive can become clogged up with numerous files that are broken up across various locations around the drive. The drive becomes really chaotic. Due to the drive getting chaotic your computer gradually slew's down in its speed as it tries to access information from files scattered all over the drive. Hence it's really important to carry out a process that rationalizes the various files from time to time. Defragmentation collects all the different parts of one file back together in one place in the hard drive. Then it in turns reorganizes information and places the files that are used most frequently. Defragmentation process leads to a much faster running computer.
Clearing your cache (cookies and Internet files) This folder cache is of temporary Internet files folder that is a record of files which have been viewed or downloaded from the web, including web pages, images, music and cookies (small files that websites can create on your computer to help them deliver personalized content when you next visit.
Automatic updating
Computer hackers are determined to destabilise computer software through their malicious programs. A number of big companies like Microsoft, 'patch' their products in order to ensure their safety. If you run on windows then make sure your computer is set to update automatically. These updates can be automated by clicking on the start then programs. Windows updates ensure that you're set to install updates automatically.
Checking for viruses
Installing some form of anti-virus software is a must. The computer is vulnerable to a range of viruses. These viruses are transmitted to your computer via infected email attachments. These viruses are called as worms and can spread over the Internet. The viruses are used by criminals in order to gather personal information. These worms can have serious consequences. Viruses have the capability of gathering financial information and secret data such as passwords and user names.
Hence making adequate arrangements of prevention is always better than cure. Installing enough antivirus protection programs for virus protection on your computers is the best way to protect your computer.
Anti- virus software can be bought as stand-alone or as a comprehensive security suite. Example of various software manufacturers include Me A fee and AVG.
Installing anti malware, spyware and adware
Malware, spyware and adware all pose a significant threat to your online privacy and the smooth-running of your computer. It is extremely essential to install along with anti-virus software, the antispyware software also. The spyware can spy on your online activities, as it installs unwanted program on your computer. Adware is used by commercial companies to find out more about consumers and track the effectiveness of their advertising, but it can have more dire consequences. Malicious adware or spyware is very hard to remove from your computer. It can cause to block access to certain websites, stop you running antivirus software, scan your hard disk and locate sensitive personal information, such as credit card numbers and other personal information which can then be used for criminal activities.
In order to ensure that you don't fall victim you can install an anti-spyware software. They work in the same way as anti-virus software. These free Downloadable products include Ad Aware and Microsoft Defender. As with anti-virus software, the free versions may not be quite as comprehensive as their paid for counterparts but they should provide a decent level of protection.
Set up a Firewall
Firewalls are a significant way of protecting your computer from some of the threats that have crept up in the cyberspace world. Firewalls are an effective way to safeguard you from hackers, viruses and worms. These viruses can endanger the personal information that is kept on your computer. Firewalls are a barrier between your computer and the world outside. But firewalls are not enough to be relied on only. They alone cannot protect your computer from online threats. Your firewall should be used in conjunction with other forms of computer security, such as your anti-virus software.
Windows packages contain a 'desktop firewall', for which you don't need to pay for and provide a basic level of security. The broadband internet router that is used for an internet connection also a firewall built into it, which can be controlled via your computer and which is password protected.
Cleaning your computer
Ensuring that your computer is clean of dust and dirt can make sure that your computer is kept under hygienic conditions. Make sure your computer is turned off and unplugged before you clean it. You can buy specialist computer cleaning products or use a damp, lint-free soft cloth to gently dislodge dirt from the keyboard or the exterior of the computer. A computer mouse is particularly susceptible to dirt, making it difficult to control. To clean your mouse turn the retaining ring on the bottom of the mouse anti-clockwise to remove the mouse ball. You can then use a clean soft cloth to remove any dust or dirt from inside the mouse.
It's important to deal with any spillages on your keyboard quickly. Turn off your computer and then turn the keyboard on its side to drain off the excess. Use a soft cloth to mop up any remaining liquid and then let your keyboard dry off before using
It again.
You need to login to perform this action.
You will be redirected in
3 sec
